The rise of the connected car has resulted in several innovative developments in the automotive sector. The modern car is more technologically advanced and linked than ever before, with new forms of car sharing and ride-hailing services, powerful entertainment systems and driver-assist technologies. However, cars are more susceptible to hacking assaults as they get more connected. Automotive hacking is a concern for both automakers and car owners in the recent years.
Automotive Hacking
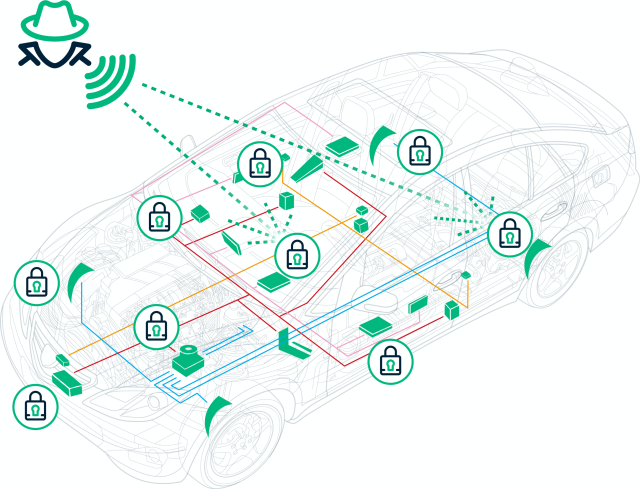
Unauthorized access to or manipulation of a car’s computer systems is referred to as automotive hacking. This might include straightforward assaults like breaking into a car or messing with the infotainment system, and sophisticated ones like taking over the steering or engine. Automotive hacking can be done physically by getting into the car’s onboard computer systems or remotely by taking advantage of weak points in the wireless network.
Data Protection Approach

Enterprise data protection experts concur that automakers must update their data security procedures to thwart attempts by hackers. Simple data protection measures like perimeter security and intrusion detection might not be enough to fend off attackers. Stronger passwords won’t be able to fend off the sophisticated tactics that attackers are using to break in. To secure data, so that even if it is stolen, the attacker cannot use it to harass the victim, the present data breach vulnerabilities need to be addressed using tokenization or encryption.
Driverless Vehicles and Ransomware
The goal of cybercriminals is to steal data from unsuspecting passengers, which they would then exploit to hold their victim’s hostage. Since connected and autonomous vehicles depend on user data for operation, this is a lucrative target. Nowadays, cybercriminals have access to enormous amounts of Personally Identifiable Information (PII) data, including a passenger’s home address, credit card number, email address, and places they travel to. Then, they can develop and send convincing phishing emails in an effort to steal more data or trick recipients into clicking on harmful links, allowing them access to the recipient’s machine. They have two options: scrape valuable data or hold it until they receive a sizable ransom payment.
Hackers’ Entry Points: Ways to Prevent Them
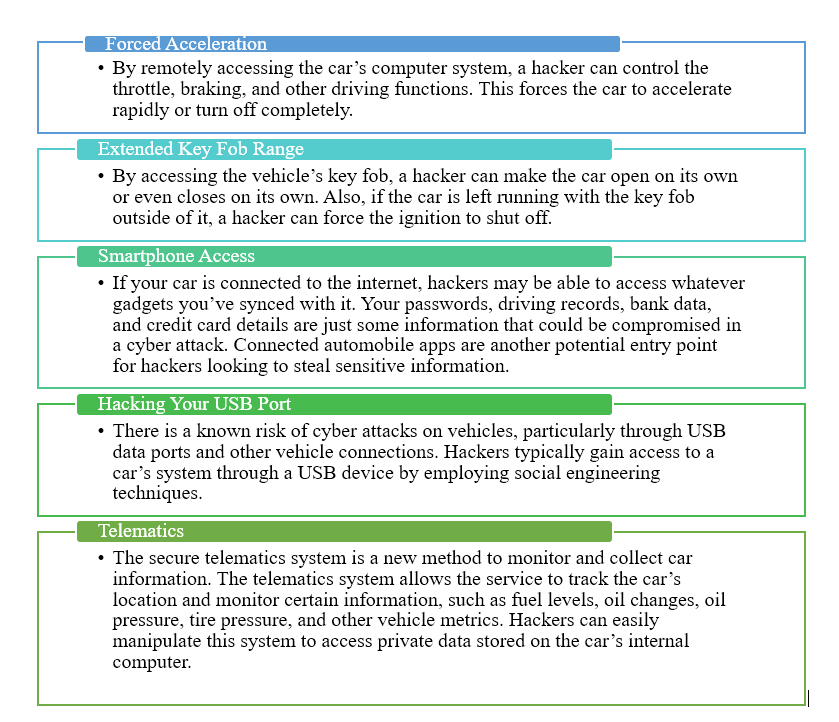
Steps to Curb these Attacks
- By taking the necessary steps, you can shield yourself from becoming a victim of a cyberattack.
-
- Maintain System Updates: In order to get the most recent bug patches, it’s critical to keep the software on your car updated. These important upgrades include security patches for the systems of the car’s known vulnerabilities. The best course of action is to closely monitor cyber security updates from your car maker because vulnerabilities emerge as a result of discoveries and patches.
- Reduced access: By creating password-protected accounts, you may restrict who has access to the data about your car. By limiting access to individuals with valid accounts, this will assist in preventing unauthorized login attempts.
- Detect and Stop Unauthorized Communications: Malicious code and data packets are frequently sent to a vehicle as the initial stage of a cyberattack. It is advised to have a firewall integrated within the car to stop hackers from accessing the internal network. Vehicle-to-vehicle (V2V) and vehicle-to-everything (V2X) communication will be limited to authorized parties by an effective firewall (vehicle-to-everything).
- Use third-party software with caution: Your car could be harmed if third-party software and programs are installed on it. Use only automaker-approved software when altering your car.
- Use of VPNs: Numerous VPNs have received favorable ratings, which demonstrates how useful they are for protecting drivers. Engine management and electronic systems in cars can be protected by VPNs. A robust VPN will enable car owners to securely access the internet while also defending linked automobiles from outside assaults. Some travelers already use a VPN to access the networks of their offices or coworking spaces.
Finally, be careful to routinely update the software on your car and apply security fixes. Make sure that any customized software on your car has the automaker’s approval. By establishing password-protected accounts, you can restrict the number of people who have access to the software in your car.There are numerous wireless and other cyber vulnerabilities in automobiles. In the automobile sector, having the correct kind of cyber security is crucial. While technology advancements may contribute to increased driver security, there is a chance that they could also make automobiles more vulnerable. Hackers can access automotive systems more easily as they grow increasingly linked. In order to safeguard all these aspects of the driving experience, automakers should concentrate on creating secure software and executing a defense-in-depth strategy that includes powerful cyber security solutions.
-
References

Author
Lakshana D
Lakshana is a part of the Red Team at GS Lab | GAVS. She is passionate about technology and spends her free time reading, traveling and gardening. She loves playing badminton and is a sports fanatic.