Security Information and Event Management (SIEM) pull together log information from all log sources (Security tools, Servers, Network devices etc.) and stores all in one place.
SIEM offers a dashboard where collected data is organized, offering a visual representation of the data. Security Analysts receive alerts when threats are detected, and these alerts can be configured to come via the dashboard or through email.
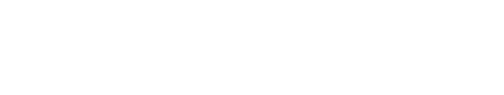
Implementing SIEM in your cybersecurity strategy offers a range of significant advantages. Here are a few of them –
1. Centralized Log Management
SIEM tools provide a centralized platform for log management, making it easier to collect, store, and search through massive amounts of security data. Log data comes in different formats and structures depending on the source. SIEM tools normalize this data, making it consistent and easily interpretable. SIEM systems can identify patterns, anomalies, and security events that may go unnoticed when examining logs individually. By correlating data, they can detect complex, multi-stage attacks that involve multiple systems. It helps organizations understand the timeline of an attack or data breach.
2. Improved Threat Detection and Response
SIEM systems collect, monitor, and analyze security data from various sources, such as network traffic, logs, and endpoints. This holistic view allows organizations to detect anomalies and potential threats in real-time. By identifying unusual patterns or unauthorized access, security teams can respond quickly and mitigate potential security incidents.
3. Compliance and Reporting
Organizations are subject to various regulatory requirements, such as GDPR, HIPAA, PCI DSS, and more. These regulations dictate specific security and privacy measures that must be in place. SIEM solutions help organizations comply with these regulations by monitoring and reporting on relevant security controls and activities. SIEM systems assist in compliance efforts by automating the collection and reporting of security-related data and reducing the risk of non-compliance.
4. Reduced False Positives
One of the significant advantages of SIEM is its ability to reduce false positives. By correlating data from multiple sources and applying sophisticated rules and algorithms, SIEM tools help security teams distinguish real threats from false alarms. This, in turn, improves the overall efficiency of incident response efforts.
5. Enhanced Incident Response
SIEM solutions not only detect threats but also facilitate faster and more effective incident response. They provide alerts and notifications to security teams, helping them take swift action. Automated incident response workflows can also be implemented, allowing organizations to respond to threats 24/7.
6. Forensic Analysis and Investigation
Forensic analysis begins with collecting data relevant to the incident. This data may include logs, network traffic records, system files, and other sources of information. SIEM systems continuously monitor for security incidents and alerts. When a potential incident is detected, it triggers an alert. Security analysts review the alerts generated by the SIEM. Forensic analysis involves the examination of the collected data to reconstruct the incident’s timeline, understand the attack vectors, and identify the root cause. Analysts try to determine the source and purpose of the attack or incident. They classify the incident as either a security breach or a false positive. Based on the findings of the forensic investigation, the incident response team takes action to contain, mitigate, and remediate the incident. This might involve isolating affected systems, patching vulnerabilities, and enhancing security controls.
7. Cost Savings
While the initial implementation of a SIEM system can be an investment, the long-term benefits often lead to cost savings. SIEM streamlines security operations, reducing the need for manual monitoring and investigation, thus saving both time and money.
8. Scalability
SIEM systems are highly scalable and can adapt to the evolving needs of an organization. As the volume of data and complexity of threats increase, SIEM can expand to accommodate these changes, ensuring that an organization’s security posture remains robust.
9. Real-time Visibility
By providing real-time visibility into network activities and security events, SIEM tools empower organizations to act proactively. This real-time insight can help identify emerging threats and vulnerabilities before they can cause significant damage.
10.User and Entity Behavior Analytics (UEBA)
Many SIEM solutions incorporate UEBA capabilities, which enable organizations to detect abnormal user and entity behavior. This helps in identifying insider threats and compromised accounts, ultimately strengthening the security posture.
11. Customization and Integration
SIEM systems can be tailored to the specific needs and technologies of an organization. They are often compatible with various security solutions and can integrate with other tools for a seamless and comprehensive security infrastructure.
SIEM plays a pivotal role in enhancing the cybersecurity posture of organizations. With its centralized log management, improved threat detection and response, compliance and reporting capabilities, and reduction of false positives, SIEM offers a comprehensive solution for safeguarding critical data and systems.
Author

Naren Raja E
Naren is a Lead SOC Engineer at GS Lab | GAVS and is interested in learning new technologies in the cybersecurity space and exploring avenues for product improvements.
Author

Sripriyadharshini A
Sripriya is a seasoned Security Operations Center (SOC) analyst with a passion for cybersecurity and a commitment to enhancing digital defenses. She enjoys exploring new cybersecurity technologies.